Introduction to Trezor Login
Trezor is one of the leading hardware wallets designed to provide secure storage for your cryptocurrency assets. Accessing your Trezor account securely is essential to protect your digital wealth. Trezor Login ensures a safe and streamlined authentication process, combining advanced encryption with user-friendly features.
This guide will cover everything you need to know about logging into your Trezor device, setting up secure access, and managing your crypto assets safely.
Why Secure Login Matters
Security is paramount in the world of cryptocurrencies. Unlike traditional banking, crypto assets are fully under your control, which means there is no central authority to recover your funds if your login is compromised. Trezor Login uses multiple layers of protection to prevent unauthorized access, including PIN codes, passphrases, and physical device verification.
By following best practices when accessing your Trezor device, you can ensure that your digital assets remain protected from phishing attacks, malware, and unauthorized logins.
Getting Started with Trezor Login
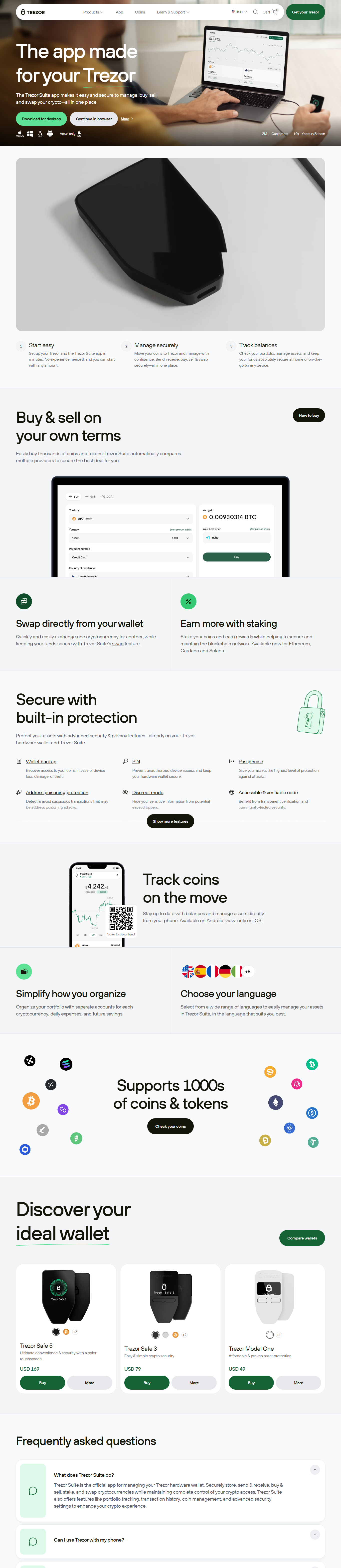
To begin using your Trezor device, first connect it to your computer or mobile device. The Trezor Suite software provides a simple interface to guide you through the login process. You will need to initialize your device if it's your first time logging in. This includes setting up a PIN code and optionally a passphrase for added security.
Once your device is initialized, you can access your Trezor wallet, manage your cryptocurrency portfolios, and execute transactions securely.
Step-by-Step Login Process
1. **Connect Your Device:** Plug your Trezor device into a USB port of your computer or connect via mobile app.
2. **Open Trezor Suite:** Launch the Trezor Suite application, which provides the login interface.
3. **Enter PIN Code:** Input your personal PIN code to unlock the device.
4. **Passphrase Verification (Optional):** If you enabled a passphrase, enter it to access your wallet securely.
5. **Access Wallet:** Once verified, you will be able to view your balances, send/receive crypto, and manage assets.
Advanced Security Features
Trezor Login integrates advanced security features such as firmware verification, device recovery, and encrypted communication. Every login is protected with end-to-end encryption, ensuring that your sensitive information is never exposed to third parties.
Additionally, Trezor’s recovery seed allows you to regain access if your device is lost or damaged, but it must be kept offline and secure at all times.
Tips for Safe Login Practices
- Always verify the website URL before logging in.
- Never share your PIN or passphrase with anyone.
- Keep your Trezor firmware up to date to prevent security vulnerabilities.
- Use a strong, unique passphrase to enhance protection.
Troubleshooting Common Login Issues
Even with a secure setup, users may encounter login issues. Common problems include device recognition errors, PIN entry mistakes, or software updates. Following the official Trezor troubleshooting guide and ensuring your system meets the software requirements will resolve most login problems.
Conclusion
Trezor Login is your gateway to managing your cryptocurrency securely. By adhering to best security practices, using strong authentication, and keeping your recovery options safe, you ensure that your digital assets remain protected. The Trezor device combined with its secure login system empowers users to take full control of their crypto without compromising safety.
Remember, consistent vigilance and responsible usage are key to maintaining the integrity of your cryptocurrency assets.